1.查壳
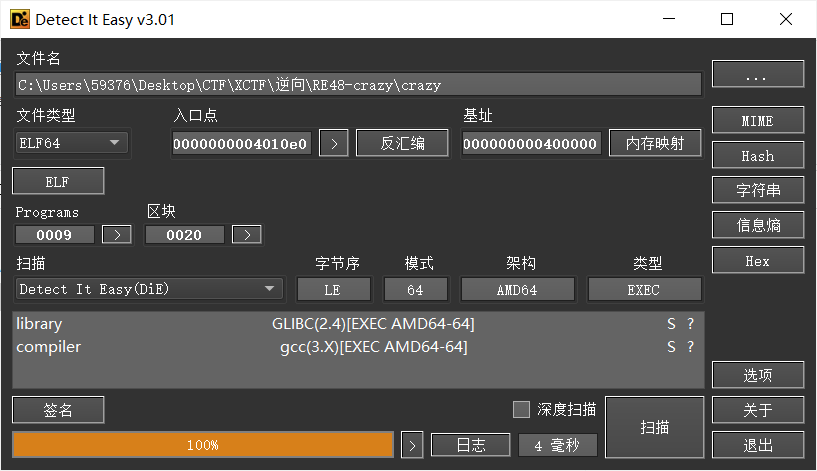
PE32 无壳
运行程序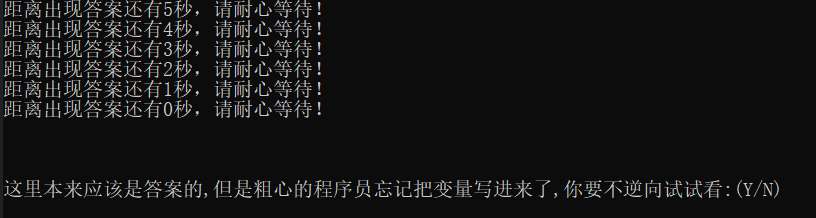
2.IDA静态分析
(1)main
// attributes: thunk
int __cdecl main(int argc, const char **argv, const char **envp)
{
return main_0(argc, argv, envp);
}跟进main_0
(2)main_0
int __cdecl main_0(int argc, const char **argv, const char **envp)
{
char v4[4]; // [esp+4Ch] [ebp-Ch] BYREF
const char *v5; // [esp+50h] [ebp-8h]
int v6; // [esp+54h] [ebp-4h]
v6 = 5;
v5 = "DBAPP{49d3c93df25caad81232130f3d2ebfad}";
while ( v6 >= 0 )
{
printf(&byte_4250EC, v6);
sub_40100A();
--v6;
}
printf(asc_425088);
v4[0] = 1;
scanf("%c", v4);
if ( v4[0] == 89 )
{
printf(aOd);
return sub_40100A();
}
else
{
if ( v4[0] == 78 )
printf(&byte_425034);
else
printf(&byte_42501C);
return sub_40100A();
}
}v5疑似flag,提交后发现成功,flag为:flag{{49d3c93df25caad81232130f3d2ebfad}}