1.查壳
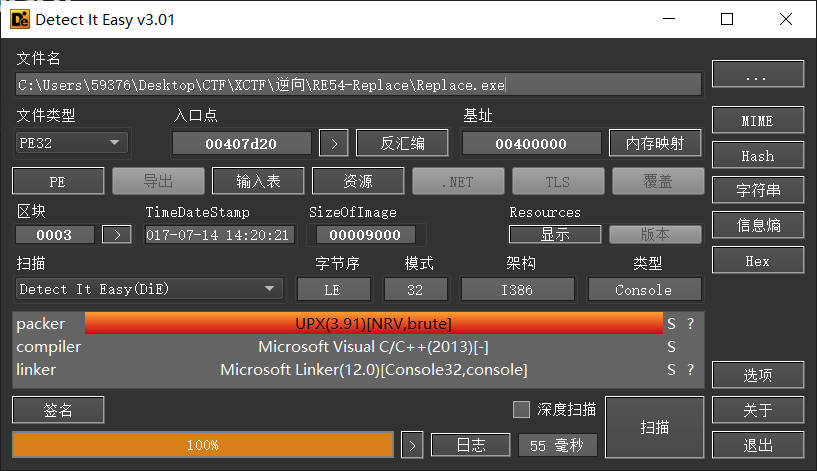
PE32 有UPX壳
运行
脱壳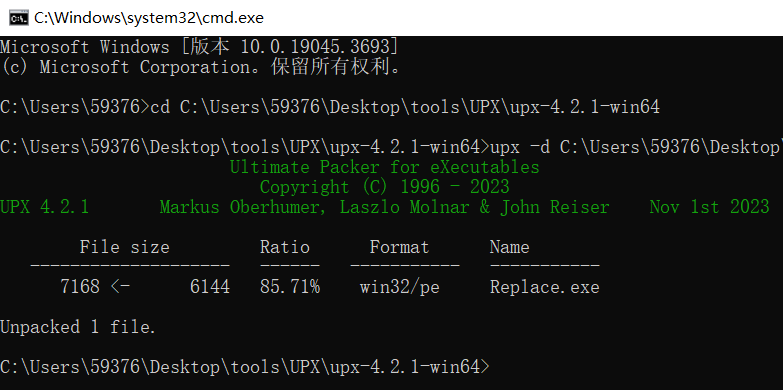
2.IDA静态分析
(1)main
int __cdecl main(int argc, const char **argv, const char **envp)
{
int v3; // kr00_4
char Buffer[40]; // [esp+4h] [ebp-2Ch] BYREF
memset(Buffer, 0, sizeof(Buffer));
printf("Welcome The System\nPlease Input Key:");
gets_s(Buffer, 0x28u);
v3 = strlen(Buffer);
if ( (unsigned int)(v3 - 35) <= 2 )
{
if ( sub_401090((int)Buffer, v3) == 1 )
printf("Well Done!\n");
else
printf("Your Wrong!\n");
}
return 0;
}程序逻辑比较简单,sub_401090为关键函数
(2)sub_401090
int __fastcall sub_401090(int a1, int a2)
{
int v4; // edx
char v5; // al
int v6; // esi
int v7; // edi
char v8; // al
int v9; // eax
char v10; // cl
int v11; // eax
int v12; // ecx
if ( a2 != 35 ) // 长度为35
return -1;
v4 = 0;
while ( 1 )
{
v5 = *(_BYTE *)(v4 + a1); // v5为输入
v6 = (v5 >> 4) % 16; // 将输入的高四位转16进制
v7 = ((16 * v5) >> 4) % 16; // v7为输入的低四位
v8 = byte_402150[2 * v4];
if ( v8 < '0' || v8 > '9' )
v9 = v8 - 87;
else
v9 = v8 - 48;
v10 = byte_402151[2 * v4];
v11 = 16 * v9;
if ( v10 < 48 || v10 > 57 )
v12 = v10 - 87;
else
v12 = v10 - 48;
if ( (unsigned __int8)byte_4021A0[16 * v6 + v7] != ((v11 + v12) ^ 0x19) )// 将输入的值作为索引,在数组byte_4021A0中取值
break;
if ( ++v4 >= 35 )
return 1;
}
return -1;
}将输入作为索引在byte_6E21A0中取值,v11和v12由题目提供的数组byte_402150和byte_402151处理得到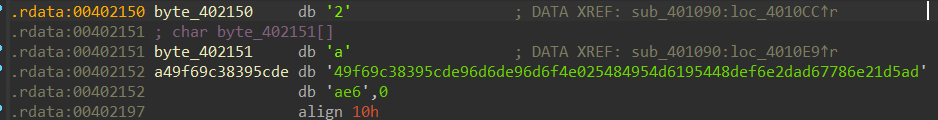
综上,此函数逻辑为:
byte_6E21A0[v5] == (v11+v12)^0x19
3.解题
python脚本如下:
byte_402150 = '2a49f69c38395cde96d6de96d6f4e025484954d6195448def6e2dad67786e21d5adae6'
byte_402151 = byte_402150[1:]
byte_4021A0 = [
0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01,
0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76, 0xCA, 0x82, 0xC9, 0x7D,
0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4,
0x72, 0xC0, 0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC,
0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15, 0x04, 0xC7,
0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2,
0xEB, 0x27, 0xB2, 0x75, 0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E,
0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84,
0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB,
0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF, 0xD0, 0xEF, 0xAA, 0xFB,
0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C,
0x9F, 0xA8, 0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5,
0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2, 0xCD, 0x0C,
0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D,
0x64, 0x5D, 0x19, 0x73, 0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A,
0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB,
0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3,
0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79, 0xE7, 0xC8, 0x37, 0x6D,
0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A,
0xAE, 0x08, 0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6,
0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A, 0x70, 0x3E,
0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9,
0x86, 0xC1, 0x1D, 0x9E, 0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9,
0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF,
0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99,
0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x16]
flag = ''
for v4 in range(35):
v8 = ord(byte_402150[2 * v4])
if v8 < 48 or v8 > 57:
v9 = v8 - 87
else:
v9 = v8 - 48
v10 = ord(byte_402151[2 * v4])
v11 = 16 * v9
if v10 < 48 or v10 > 57:
v12 = v10 - 87
else:
v12 = v10 - 48
t = byte_4021A0.index((v11 + v12) ^ 0x19)
flag += chr(t)
print(flag)运行结果:
flag{Th1s_1s_Simple_Rep1ac3_Enc0d3}